How DNS Resolution Works
Topics that we are going to cover in this blog are mentioned below…
What is DNS and why name resolution exists?
What is the
digcommand and when it is used?Understanding
dig . NSand root name serversUnderstanding
dig com NSand TLD name serversUnderstanding
dig google.com NSand authoritative name serversUnderstanding
dig google.comand the full DNS resolution flow
What is DNS?
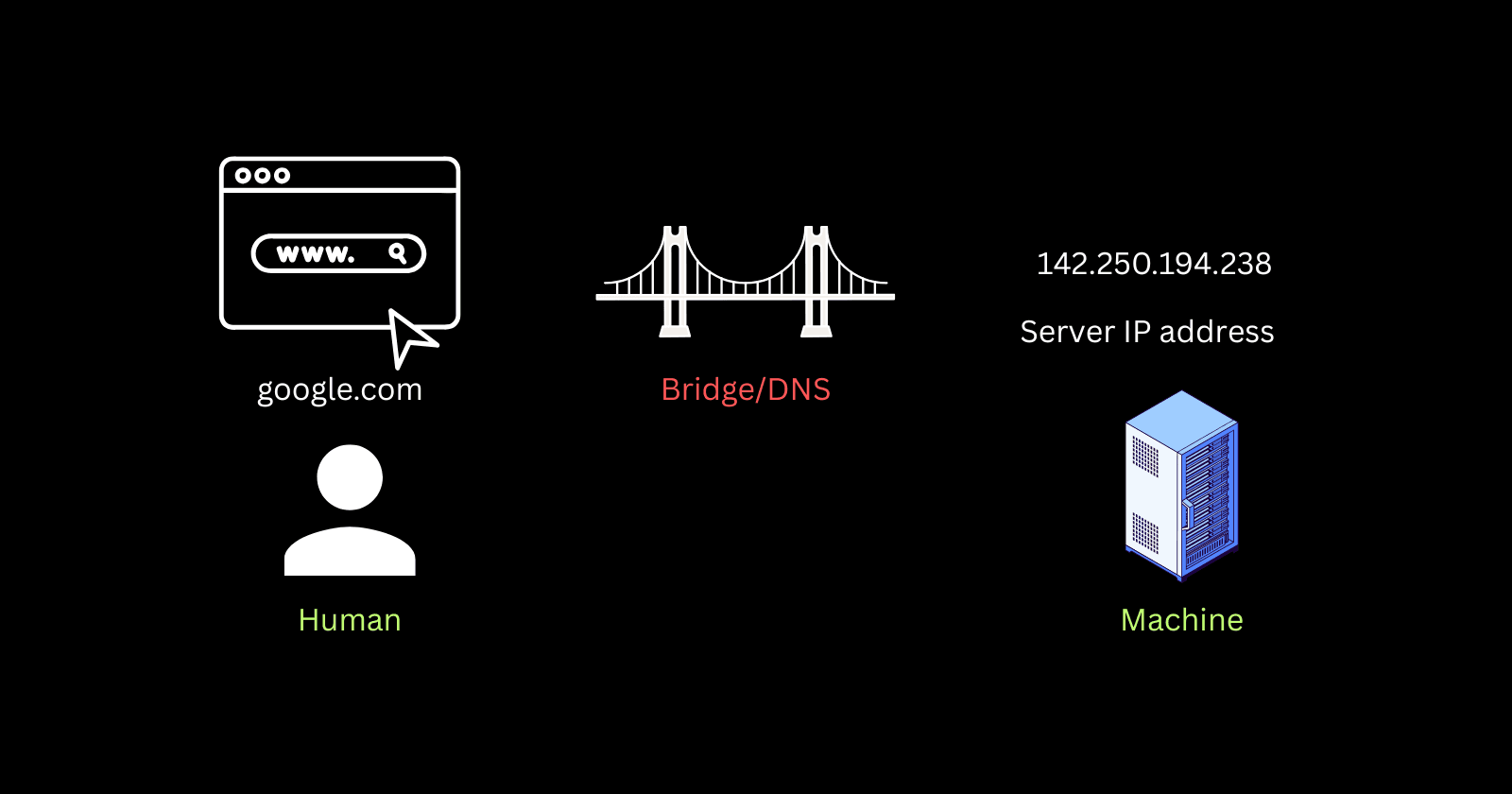
DNS stands for Domain Name System, before driving deep inside the technical. Let’s understand this in simple way.
We humans are not good in memorising the numbers but good in remembering the names, as we named everything ie humans names Rohit, Sunil etc whereas on the otherside machines are good in understanding the numbers rather than names. So, to bridge this gap between humans and machines DNS comes into the picture whose one of the main functions is to convert the input given by humans in name type into the numerical value type (IP) for the machines to address them and give the response back to the humans.
The DNS resolution is something like the phonebook/contact list in phone, where we generally search for names and get the number. So, DNS is very essential to translate the human readable text to machine readable IP addresses.
What is ‘dig’ command and when it is used?
dig stands for Domain Information Groper which is a powerful administrator command line tool used to querry the DNS servers to troubleshoot,diagnose and verify domain configurations.
There is also a similar command to dig which is nslookup which also use for querry the DNS but the key difference between these two commands is, dig uses the operating system DNS querry library where as nslookup doesn’t use the library.
We use dig command to get the information of the DNS in various ways like knowing the DNS recode ie A, CNAME,NS,MX etc we will see what are records in next blog. So, basically we use dig for basic lookup, querry DNS records, querry DNS server, trace route , short answer only.
dig google.com --> will give the IP in 'A' type DNS record.
dig google.com CNAME --> will give the DNS CNAME record details specificaly.
dig google.com +short --> will just give you IP address nothing else.
dig @IP_of_other_DNS google.com --> used when you want to check the other’s DNS server.
Understanding dig . NS and root name server?
If we understand the command here dig . NS, dig is command - whereas ‘dot’ means root - and NS means the Name Server which is a DNS Record.
Let’s see the flow of the command…
'dig' will start to find the root server (.) after that NS is called which mean authoritative
server (main authority)
And we will see the output on the terminal as a list of 13 Root server which is spread
accross the world and controlled and managed by 12 different organisations.
___LIST OF 13 SERVERS___
51xxxx IN NS a.root-servers.net.
. 51xxxx IN NS b.root-servers.net.
. 51xxxx IN NS c.root-servers.net.
. 51xxxx IN NS d.root-servers.net.
. 51xxxx IN NS e.root-servers.net.
. 51xxxx IN NS f.root-servers.net.
. 51xxxx IN NS g.root-servers.net.
. 51xxxx IN NS h.root-servers.net.
. 51xxxx IN NS i.root-servers.net.
. 51xxxx IN NS j.root-servers.net.
. 51xxxx IN NS k.root-servers.net.
. 51xxxx IN NS l.root-servers.net.
. 51xxxx IN NS m.root-servers.net.
-----COMMENTS TO READ-----
// Don't think to much as for now we will see the flow diagram later in this blog.
Understanding dig com NS command
This is another important dig command to get the information about the TLD Servers (TOP LEVEL DOMAIN) ie .com,.org etc. Root Servers directs the traffic to TLD for more information.
___TLD Servers___
d.gtld-servers.net.
h.gtld-servers.net.
m.gtld-servers.net.
a.gtld-servers.net.
j.gtld-servers.net.
i.gtld-servers.net.
e.gtld-servers.net.
f.gtld-servers.net.
b.gtld-servers.net.
k.gtld-servers.net.
l.gtld-servers.net.
g.gtld-servers.net.
c.gtld-servers.net.
Understanding dig google.com NS and Authoritative Server
Here dig command is further driving deep inside the TLD Server (.com extension) to locate the authoritative server(google, in this command) which holds all the details ie IP address of the domain google.com
___YOU WILL SEE THE DETAILS OF AUTHORITATIVE SERVER___
ns3.google.com. 108149 IN A 216.239.36.10
ns2.google.com. 345463 IN A 216.239.34.10
ns4.google.com. 63718 IN A 216.239.38.10
FLOW DIAGRAM of DNS Resolution

Let’s understand this diagram…
When a user or client searches for something like zerodha.com, the browser contacts a helper called the Resolver Server, which does all the work for the browser. The resolver first goes to the Root server. The Root server checks the extension, like .com, and sends the request to the TLD server. Then, the resolver goes to the TLD server, which looks for the authoritative server, in this case, zerodha. Finally, the resolver moves to the authoritative server, gets the IP address of zerodha.com, and provides it to the browser. Now, your screen displays the landing page of Zerodha.
Conclusion
Understanding the behind the scene of a tech is wonderfull and the more you deep drive the more you get to know the interesting facts about them.